by Shawn Bower
Introduction
When working on your custom application at Cornell the primary option for integrating authentication with the Cornell central identity store is using Cornell’s Shibboleth Identity Provider (IDP). Using Shibboleth can help reduce the complexity of your infrastructure and as an added bonus you can enable access to your site to users from other institutions that are members of the InCommon Federation.
How Shibboleth Login Works
Key Terms
- Service Provider (SP) – requests and obtains an identity assertion from the identity provider. On the basis of this assertion, the service provider can make an access control decision – in other words it can decide whether to perform some service for the connected principal.
- Identity Provider (IDP) – also known as Identity Assertion Provider, is responsible for (a) providing identifiers for users looking to interact with a system, and (b) asserting to such a system that such an identifier presented by a user is known to the provider, and (c) possibly providing other information about the user that is known to the provider.
- Single Sign On (SSO) – is a property of access control of multiple related, but independent software systems.
- Security Assertion Markup Language (SAML) – is an XML-based, open-standard data format for exchanging authentication and authorization data between parties, in particular, between an identity provider and a service provider.
- A user request a resource from your application which is acting as a SP
- Your application constructs an authentication request to the Cornell IDP an redirects the user for login
- The user logins in using Cornell SSO
- A SAML assertion is sent back to your application
- Your application handles the authorization and redirects the user appropriately.
Shibboleth Authentication for Your Application
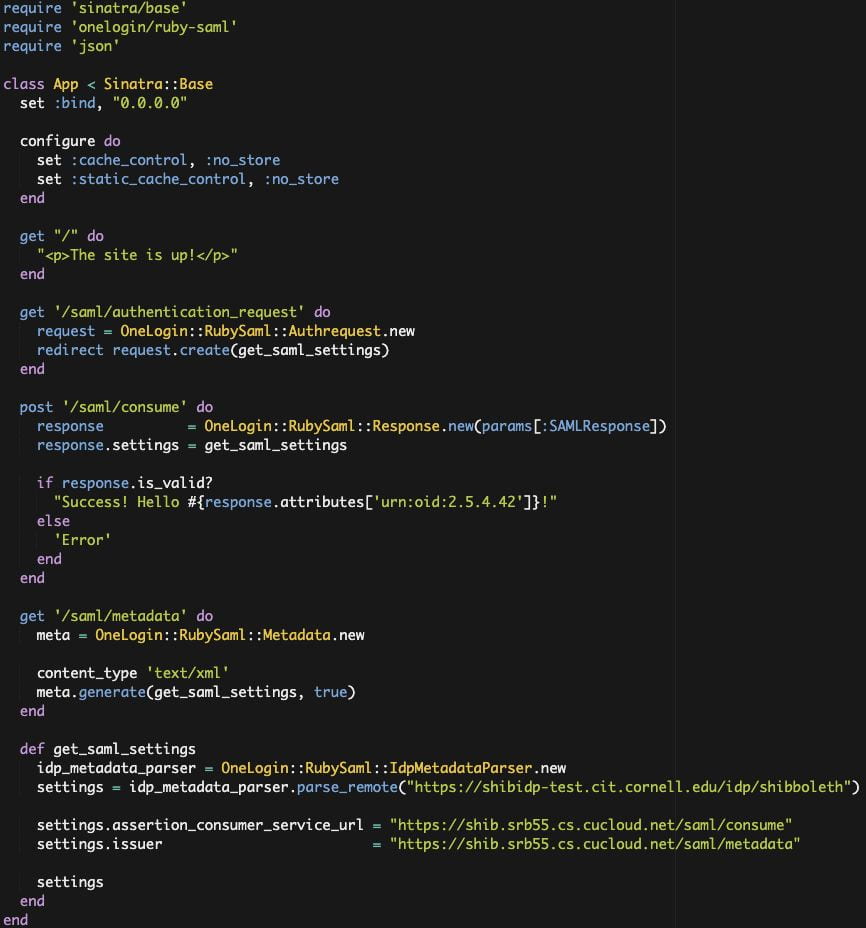
Your application will act as a service provider. As an example I have put together a Sinatra application in ruby that can act as a service provider and will use the Cornell Test Shibboleth IDP. The example source can be found here. For this example I am using the ruby-saml library provided by One Login, there are other libraries that are compatible with Shibboleth such as omniauth. Keep in mind that Shibboleth is SAML 2.0 compliant so any library that speaks SAML should work. One reason I choose the ruby-saml library is that the folks at One Login provide similar libraries in various other languages, you can get more info here. Let’s take a look at the code:
First it is important to configure the SAML environment as this data will be needed to send and receive information to the Cornell IDP. We can auto configure the IDP settings by consuming the IDP metadata. We then have to provide an endpoint for the Cornell IDP to send the SAML assertion to, in this case I am using “https://shib.srb55.cs.cucloud.net/saml/consume.” We also need to provide the IDP with an endpoint that allows it to consume our metadata.
We will need to create an endpoint that contains the metadata for our service provider. With OneLogin::RubySaml this is super simple as it will create it based on the SAML settings we configured earlier. We simply create “/saml/metadata” which will listen for get request and provided the auto generate metadata.
Next lets create an endpoint in our application that will redirect the user to the Cornell IDP. We create “/saml/authentication_request” which will listen for get requests and then use the OneLogin::RubySaml to create an authentication request. This is done by reading the SAML settings which include information on the IDP’s endpoints.
Then we need a call back hook that the IDP will send the SAML assertion to after the user has authenticated. We create “/saml/consume” which will listen for a post from the IDP. If we receive a valid response from the IDP then we will create a page that will display a success message along with the first name of the authenticate user. You might be wondering where “urn:oid:2.5.4.42” comes from. The information returned in the SAML assertion will contain attributes agreed upon by InCommon as well as some attributes provided by Cornell. The full list is:
|
AttributeNameInEnterpriseDirectory
|
AttributeNameInSAMLAssertion
|
|---|---|
| edupersonprimaryaffiliation | urn:oid:1.3.6.1.4.1.5923.1.1.1.5 |
| commonName | urn:oid:2.5.4.3 |
| eduPersonPrincipalName (netid@cornell.edu) | urn:oid:1.3.6.1.4.1.5923.1.1.1.6 |
| givenName (first name) | urn:oid:2.5.4.42 |
| surname(last name) | urn:oid:2.5.4.4 |
| displayName | urn:oid:2.16.840.1.113730.3.1.241 |
| uid (netid) | urn:oid:0.9.2342.19200300.100.1.1 |
| eduPersonOrgDN | urn:oid:1.3.6.1.4.1.5923.1.1.1.3 |
| urn:oid:0.9.2342.19200300.100.1.3 | |
| eduPersonAffiliation | urn:oid:1.3.6.1.4.1.5923.1.1.1.1 |
| eduPersonScopedAffiliation | urn:oid:1.3.6.1.4.1.5923.1.1.1.9 |
| eduPersonEntitlement | urn:oid:1.3.6.1.4.1.5923.1.1.1.7 |
Conclusion
We covered the basic concepts of using Shibboleth and SAML creating a simple demo application. Shibboleth is a great choice when looking at architecting your custom application in the cloud, as it drastically simplifies the authentication infrastructure while still using Cornell SSO. An important note is that in this example we used the Cornell Test Shibboleth IDP which allows us to create an anonymous service provider. When moving your application into production you will need to register your service provider from https://shibrequest.cit.cornell.edu. For more information about Shibboleth at Cornell please take a look at IDM’s Confluence page.
This article was updated May 2021 to remove outdated information.